Career Benefits Of AWS And DevOps Certifications
DevOps is one of the areas of the IT sector that is expanding the fastest right now. Operations teams and software engineers integrate their roles and efforts to create solutions that operate more quickly with improved security and efficiency.
A DevOps certification verifies your expertise and understanding while improving your career and earning potential. A globally recognized certificate next to your name paves the way for more challenging professional prospects. Most DevOps positions rank among the highest-paying technical jobs available today.
For those working in DevOps, various professional credentials are now accessible. While each assesses your technical knowledge, they fall short of developing or evaluating the non-tangible abilities you need for the job, such as teamwork and communication. Therefore, selecting the ideal DevOps certification for 2022 is crucial. Businesses could benefit significantly from AWS certifications. By having more personnel with AWS qualifications, companies may be able to join the AWS partner program. You should now check out our AWS Training in Chennai to advance your quest for a rewarding profession because an AWS certification offers so much!
Let’s first discuss the advantages of AWS certification before moving on. Let’s begin by providing a brief definition of AWS. Over 100 cloud services are included in the cloud platform known as Amazon Web Services (currently, they have more than 1000 services). The use of computing, security, databases, storage and many other resources is made possible by cloud services for businesses.
The benefit of using AWS is that businesses only have to pay for the services they utilise. Companies can build comprehensive infrastructure with the use of AWS services. Businesses can run programs without the requirement for hardware, thanks to the complete application environments. Companies can cut costs while maintaining the flexibility of their operations.
The size of the global DevOps market was projected to be USD 4,311.95 million in 2020 and USD 5,114.57 million in 2021. By 2026, it is anticipated to increase at a compound yearly growth rate of 18.95% to reach USD 12,215.54 million.[1]
Benefits Of Getting An Aws Certification
We now have a clear understanding of what AWS is and the many capabilities it offers consumers. After examining the causes of the increased demand for AWS certification tests, we will begin discussing the advantages of AWS certifications. Currently, Amazon Web Services (AWS) dominates the market for cloud service providers. Why? It offers businesses services that are affordable. The AWS services are adaptable and perfect for various business sizes.
Most importantly, AWS adheres to strict security protocols for guarding, maintaining, and monitoring its data centres. AWS continues to lead the pack of cloud service providers as a result. The status of AWS is the first justification for pursuing AWS certifications. Choose the leader if you wish to devote time and energy to learning about cloud technology.
Here is some information on Google trends that show how the demand for AWS certification is rising: AWS certification candidates must go through in-depth study materials and practical training. Recertification for AWS certifications is required every two years. Recertification validates that credentialed personnel are aware of changes and developments in the AWS market. These arguments answer the question, “Is AWS certification worth it?”. It is now appropriate to consider the advantages of various AWS certifications.
Preparing For The Future
The first benefit of an AWS certification is the rising recognition of cloud computing. According to recent studies, 83% of enterprise workloads will move to the cloud by 2020. As is common knowledge, AWS dominates the market for cloud service providers.
As a result, the benefits of AWS certification might aid in your preparation for emerging trends in the employment of IT specialists. AWS has a market share of about 31%, and its revenue is gradually increasing. Soon, the vast majority of businesses would require AWS-trained personnel. Taking an AWS certification course could help you demonstrate your talents to potential employers and improve your marketability for jobs.
New Avenues For Developing Professional Expertise
The advancement of professional knowledge is the following entry on the top AWS certification advantages list. As was previously mentioned, attaining an AWS certification takes extensive reading, practice, and dedication to mastering AWS technology. Furthermore, applicants must keep up with the most recent AWS trends to avoid issues with recertification. To obtain the certification, you must demonstrate your skill and work hard to keep it.
Individuals could get additional AWS certifications to diversify their skill set. No AWS professional is required to perform one role exclusively. After passing the AWS Developer associate test, you could pursue the AWS DevOps certification.
Gain An Appreciation For Your Efforts
Recognizing certified experts is a significant benefit of obtaining an AWS certification. Professionals with AWS certifications earn digital badges. You can use these digital badges in your email signature and social media to indicate your certification success. Instant access to special certification events sponsored by AWS is made possible via digital badges. Digital badges are also helpful in gaining admission to AWS re Invent AWS Certification Lounges and specific AWS Summit events.
With an AWS certification, you will also be invited to local appreciation receptions. You can now discover the answer to the question, “Is AWS Certification Worth It?” Any person would want to receive the kind of acclaim that comes with an AWS certificate. For instance, a professional in machine learning can pursue the AWS Machine Learning certification. Still, a professional in data analytics should pursue the AWS Data Analytics certification to certify their knowledge and further their careers.
Display Your Commitment Levels
The benefits of AWS certification are also included in the evidence of your dedication. Candidates applying for AWS certifications typically put in much more time and effort to pass the examinations. However, the candidates first demonstrate their commitment to the AWS platform by selecting AWS certifications. An AWS certification demonstrates a professional’s dedication to the AWS platform.
The road to AWS certification is a complex one. Therefore, those who are successful in earning an AWS certification must have put in a lot of effort. As a result, the accreditation denotes the professionalism of certified individuals.
Limited Difficulties To Clear AWS Certification
The convenience of the AWS certification, as compared to other certifications, is another benefit. AWS credentials, which were first introduced in 2013, have made it easier for potential candidates. Several available resources can assist you in getting the desired certification. Candidates can get AWS certified with documentation, whitepapers, and instructor-led training sessions.
The other types of training, such as digital and virtual training, offer practical experience with the foundational AWS services. To prepare for an AWS certification exam, candidates can access a variety of sample questions and practice exams. Therefore, many hopefuls would appreciate the flexibility in acquiring AWS certification!
5 In-Demand DevOps Certifications
The appropriate DevOps certification for you will rely on your sector, current market trends, and experience level. There are many DevOps certificates available. The following list includes five of the most prestigious and frequently demanded DevOps certifications by employers:
AWS Certified DevOps Engineer – Professional
Employers can verify your ability to deploy and test AWS applications and infrastructure by looking at this certification from Amazon Web Services. Additionally, it demonstrates your proficiency with cloud platforms in general, including the implementation and automation of governance procedures, security controls, and compliance validation.
The most popular cloud computing platform is AWS. With over 32,000 AWS-certified DevOps engineer jobs being advertised in the United States on Indeed in November 2022, AWS certification is one of the most in-demand certifications.
Who it’s for DevOps professionals who utilise cloud computing, particularly in an Amazon Web Services (AWS) setting
Two or more years of experience working in AWS environments and the capacity to program in a high-level programming language are recommended.
Certified Kubernetes Administrator (CKA)
A well-liked open-source framework for managing workloads and services, Kubernetes is based on containers. Obtaining CKA certification proves your ability to install and operate production-grade Kubernetes clusters. Your knowledge of Kubernetes troubleshooting, cluster architecture, installation and configuration, services and networking, workloads, scheduling, and storage will be tested.
Who it’s for IT managers of Kubernetes instances, such as cloud administrators and Kubernetes administrators
Recommended background: Basic familiarity with Kubernetes
Docker Certified Associate (DCA)
Docker is a technology that makes it easier to develop and distribute container-based software and programming projects. A benefit of having Docker certification is that it is one of the top container runtime systems.
Your knowledge of orchestration, image creation, management, registry, installation, configuration, networking, security, storage, volumes, and Docker and containers, in general, will be confirmed.
Puppet Certified Professional
Puppet is a process automation tool used by DevOps workers to speed up the delivery of infrastructure upgrades and improve software quality. Server setup can be automated and managed with the system management tool puppet software.
The Puppet Certified Professional exam assesses both your technical knowledge and practical experience. Thus passing it verifies your ability to use Puppet IT automation tools. You’ll be required to comprehend and apply ideas linked to categorization tactics, debugging Puppet code, module creation, orchestration and task management, environments, administration, language, and concepts.
Who it’s for IT specialists and DevOps engineers
Recommended background: Basic knowledge of and proficiency with Puppet
Microsoft Certified: DevOps Engineer Expert
This certification, formerly known as Azure DevOps Engineer Expert, proves your proficiency with DevOps procedures, mainly “working with people, processes, and technologies to consistently create business value”..
Creating instrumentation tactics, site reliability engineering techniques, and security and compliance plans are a few of the talents that will be evaluated. Additionally, you’ll demonstrate your proficiency in managing source control, fostering communication and cooperation, and putting continuous integration and management techniques into practice.
For DevOps engineers only: Expertise with Azure administration or development, as well as knowledge of both, is recommended. The prerequisite is the Microsoft Certified: Azure Administrator Associate or the Microsoft Certified: Azure Developer Associate Certification.
Conclusion
AWS is the cloud technology of the future, to sum up. Along with Azure and Google Cloud, AWS is well-known in the cloud service provider industry. It makes sense that becoming ready for future developments in the cloud computing employment market would be beneficial. We should also consider promising chances for a pay boost and more significant employment.
Additionally, having an AWS certification guarantees that professionals participate in the larger AWS community. In addition to establishing an AWS professional’s credentials, AWS certification also provides opportunities to grow one’s professional network. Along with these benefits, the requirements for recertification for AWS certification also guarantee ongoing professional growth.
Reference
https://www.strongdm.com/blog/devops-statistics [1]
Author Bio

Ramya K is a Content Crafter at Multiple companies with several projects; her career-related blog never fails to motivate students. Students are able to ease their future careers easily. Get in touch for more educational content.

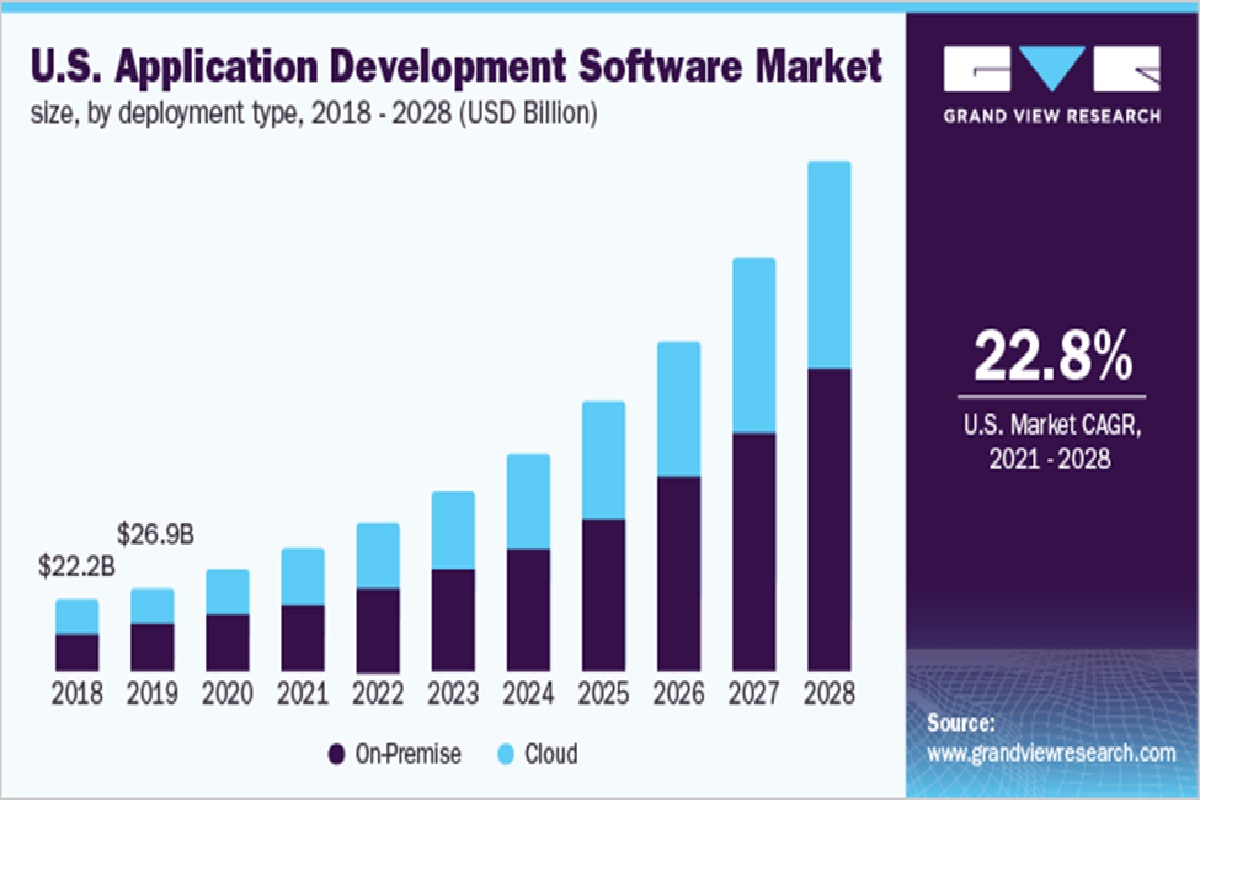 Source: Grand View Research
Source: Grand View Research






















